In today’s era, we are much more concern about privacy, but we still use unsafe means to make communication. All the bad guys out there are waiting for our personal data to be accessible or leaked to them. Here comes BLEEP, our privacy friend.
Shadow IT, or the event where technology related activities or developments are conducted outside of and without the knowledge of the enterprise IT team, is one of the phenomenon that has gained prominence in recent years.
It was two weeks ago. I was chatting with the CFO of a major automobile manufacturing company. This is one of the largest companies in the world. I was waxing eloquent… Read more »
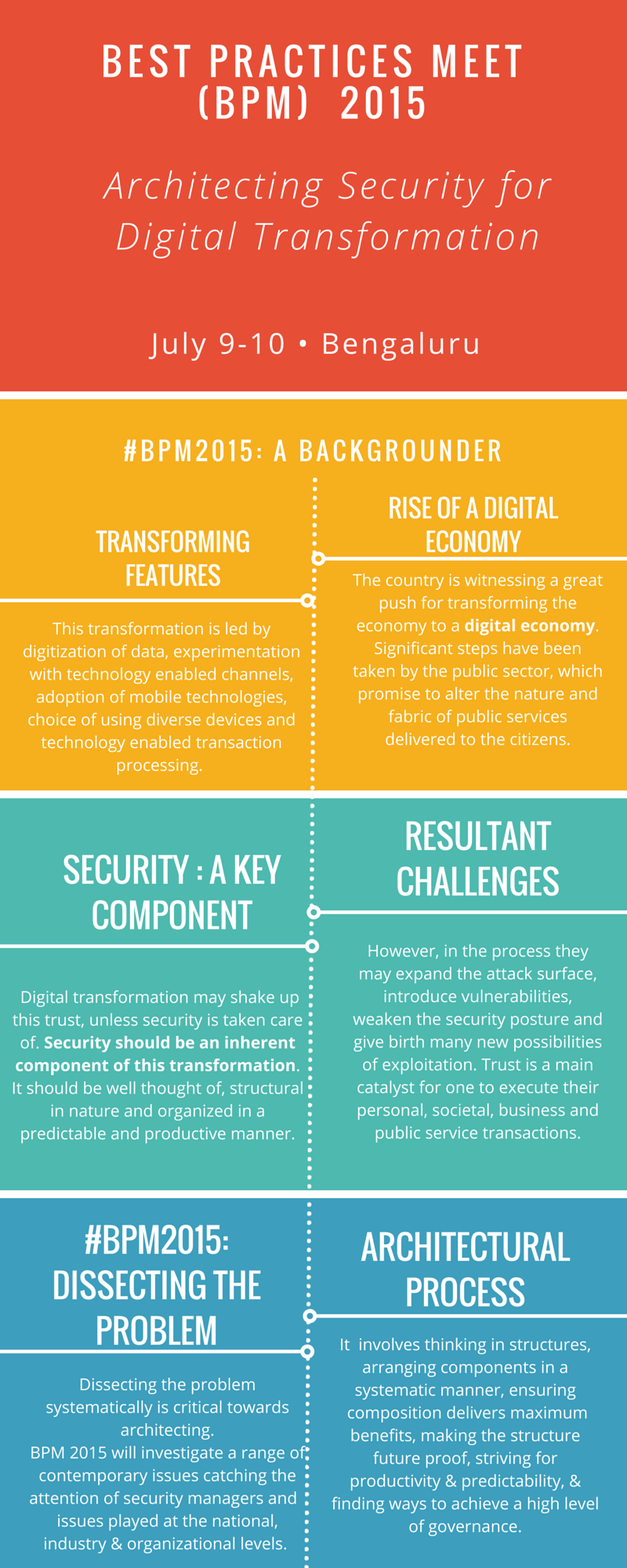
Register for the annual DSCI Best Practices Meet 2015 here. Know more: http://bit.ly/1INAMeV
Information Security is a critical facet of the modern enterprise that is riven with uncertainty and a growing list of possible threats. Building a solid information security team (own or outsourced) is critical.
Data is at the heart of everything today, but what are its implications? Shivangi Nadkarni,Co-founder & CEO, Arrka Consulting on why you should be bothered.